In one of my applications, I came through a requirement where I need to invoke a web service which is secured through SSL (implemented in .Net). This web service is from some external team and they have their own internal security.
To invoke this service from our adf application ((Jdev 11.1.1.7) and weblogic 11g server), we need to do the following steps :
I need to use JAVA SSL logic as below :
try {
TrustManager[] trustAllCerts = new TrustManager[] {
new X509TrustManager() {
public java.security.cert.X509Certificate[] getAcceptedIssuers() {
return null;
}
public void checkClientTrusted(X509Certificate[] certs, String authType) { }
public void checkServerTrusted(X509Certificate[] certs, String authType) { }
}
};
SSLContext sc = SSLContext.getInstance(“SSL”);
sc.init(null, trustAllCerts, new java.security.SecureRandom());
HttpsURLConnection.setDefaultSSLSocketFactory(sc.getSocketFactory());
HostnameVerifier allHostsValid = new HostnameVerifier() {
public boolean verify(String hostname, SSLSession session) {
return true;
}
};
// Install the all-trusting host verifier
HttpsURLConnection.setDefaultHostnameVerifier(allHostsValid);
/*
* They have 2 -way secure mechanism, 1st we need to retrieve token to access the service using the code below
*/
URL url = new URL(“https://TEST.org/connect/token”);
HttpURLConnection conn = (HttpURLConnection)url.openConnection();
conn.setDoOutput(true);
conn.setRequestMethod(“POST”);
conn.setRequestProperty( “Content-Type”, “application/x-www-form-urlencoded” );
conn.setConnectTimeout(1000000);
String urlParameters = “grant_type=test_params&scope=testapi&client_id=test_param&client_secret=test”;
byte[] postData = urlParameters.getBytes(“UTF-8”);
conn.getOutputStream().write(postData);
BufferedReader in = new BufferedReader(
new InputStreamReader(conn.getInputStream()));
String inputLine;
StringBuffer resp = new StringBuffer();
while ((inputLine = in.readLine()) != null) {
resp.append(inputLine);
}
in.close();
JSONObject obj = (JSONObject)new JSONParser().parse(resp.toString());
we get the security token in obj.
Again below code to access the actual web service by sending the token as parameter :
try {
TrustManager[] trustAllCerts = new TrustManager[] {
new X509TrustManager() {
public java.security.cert.X509Certificate[] getAcceptedIssuers() {
return null;
}
public void checkClientTrusted(X509Certificate[] certs, String authType) { }
public void checkServerTrusted(X509Certificate[] certs, String authType) { }
}
};
SSLContext sc = SSLContext.getInstance(“SSL”);
sc.init(null, trustAllCerts, new java.security.SecureRandom());
HttpsURLConnection.setDefaultSSLSocketFactory(sc.getSocketFactory());
HostnameVerifier allHostsValid = new HostnameVerifier() {
public boolean verify(String hostname, SSLSession session) {
return true;
}
};
// Install the all-trusting host verifier
HttpsURLConnection.setDefaultHostnameVerifier(allHostsValid);
/*
* end of the fix
*/
URL url = new URL(“https://test/api/Request/GetByNumber/1700594”);
HttpURLConnection conn = (HttpURLConnection)url.openConnection();
conn.setDoOutput(true);
conn.setRequestMethod(“GET”);
conn.setRequestProperty(“authorization”, “Bearer ” + token);
conn.setRequestProperty(“accept”, “application/json”);
conn.setRequestProperty(“cache-control”, “no-cache”);
int responseCode = conn.getResponseCode();
System.out.println(“\nSending ‘GET’ request to URL : ” + url);
System.out.println(“Response Code : ” + responseCode);
BufferedReader in = new BufferedReader(
new InputStreamReader(conn.getInputStream()));
String inputLine;
StringBuffer response = new StringBuffer();
while ((inputLine = in.readLine()) != null) {
response.append(inputLine);
}
in.close();
JSONObject obj = (JSONObject)new JSONParser().parse(response.toString());
String status = (String)obj.get(“Status”);
System.out.println(“status “+status);
JSONArray rooms = (JSONArray)obj.get(“Rooms”);
Iterator iterator = rooms.iterator();
while (iterator.hasNext()) {
JSONObject roomInfo = (JSONObject)iterator.next();
This JSON array is the sample code we have used in our application to get the data from the web service and to create rows and display in our adf table.
For this we need to set the proxy settings in Jdeveloper to bypass the security while running in jdev.
Preferences –> Web Browser and Proxy –>
Check Http Proxy server and specify the proxy host details and exceptions.
This setting is fine while running in local jdev.
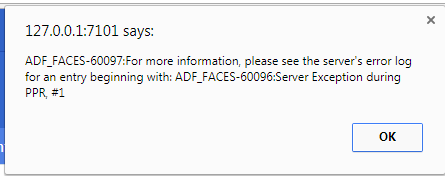
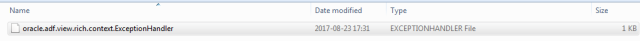
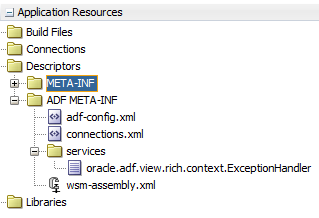
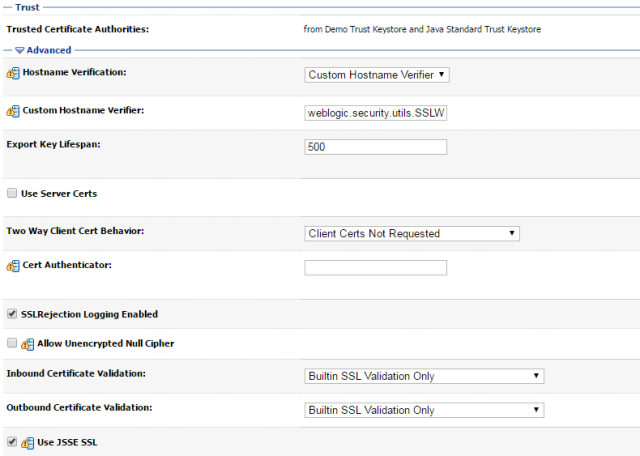
When we deploy this adf application on web logic, we got another issue related to weblogic security.
javax.net.ssl.SSLKeyException: FATAL Alert:BAD CERTIFICATE – A Corrupt and unuseable certificate was received.
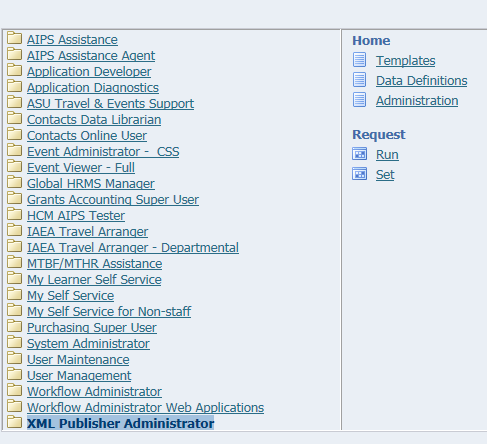
To resolve this we need to do some configuration in weblogic admin console :
Environment –> Servers –> Integration/Admin server –> SSL –> Advanced –>
Hostname Verification : Custom Hostname verifier
Custom Hostname Verifier: weblogic.security.utils.SSLWLSWildcardHostnameVerifier
Like below :
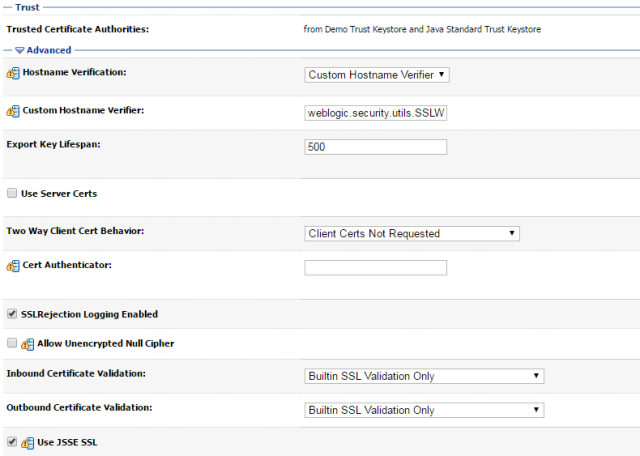
Thats enough. We could invoke SSL secured webservice from ADF web application.